Configuring SAML in Thycotic Secret Server

Before jumping into the configuration part let us understand the requirement of this integration.
Overview
if you are not familiar with what is Thycotic Secret Server. Then refer to their website https://thycotic.force.com.
Secret Server is an easy-to-use password management tool that enables you to start managing privileged accounts fast, and what is the use of securing privilege account if you may ask then it is necessary to reduce risk by eliminating unnecessary local admin privileges, blocking privileged credential theft attempts and ransomware attacks, auditing malicious behavior and strengthening the security of privileged accounts.
Integration Overview
Secret Server allows the use of SAML Identity Provider (IdP) authentication instead of the normal authentication process for single sign-on (SSO). To do this, Secret Server acts as a SAML Service Provider (SP) that can communicate with any configured SAML IdP.

In our article I am configuring Microsoft Azure Active Directory in Thycotic Secret Server.
Prerequisites : Azure portal subscription/trial and Thycotic secret server trial
Configuration Steps
1. Log into your portal.azure.com account
2. Navigate to Azure Active Directory

3. Navigate to Enterprise Applications

4. Select New Application

5. Then Click on Create your own application
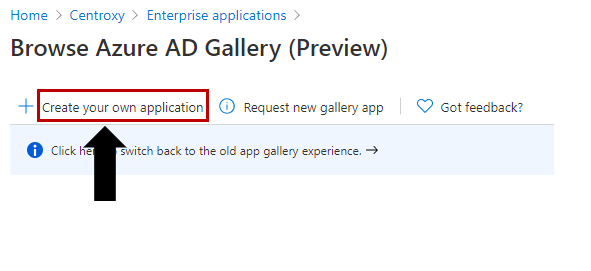
6. Give your new IDP application a name and click Add. Then enter select the “integrate any other application you don’t find in the gallery” option and select create

7. Click Single sign-on

8. In the dropdown, select SAML-based Sign-on

9. Click Upload metadata file and upload the Secret Server Metadata file previously downloaded in the SAML 2.0 Configuration Guide.(i.e the file that we generate when we Configure Thycotic Secret Server AD service).Follow the below steps to generate the metadata file.
Administer Configuration SAML Role Permission
The “Administer Configuration SAML” role permission is required to use SAML to access SS. To grant a user this permission from an administrator account:
9.1. Go to Admin > Roles. The Roles page appears.
9.2 . Click the Create New button. The Role Edit page appears:

9.2.1. Type the name, such as SAML, in the Role Name text box.
9.2.2. Click to select the Enabled check box.
9.2.3. Click Administer Configuration SAML in the right side Permissions Unassigned list box.
9.2.4. Click the < button to move the permission to the other side.
9.2.5. Click the Save button. The Roles page returns.
9.2.6. Click the Assign Roles button.name link of the newly created role. The View Role Assignment page appears:

9.2.7. Click the Role dropdown list to select the role you just created.

9.2.8. Click the Edit button. The Role Assignment page appears:
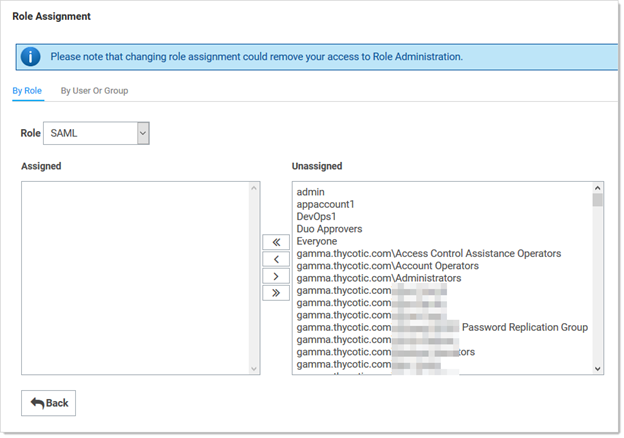
9.2.9. Move the desired users to the Assigned list using the same method as before.
9.2.10.Click the Save Changes button.
Setting up Secret Server
1. Navigate to Admin > Configuration.
2. Click the SAML tab:

3. Click the Edit button in the SAML General Settings section.
4. Click to select the SAML Enabled check box.
5. Click the Save button.
6. Under General Settings, click Edit, then check the SAML Enabled checkbox. Save changes.
7. Click the Edit button in the SAML Service Providers section.
8. Type a name for your SS service provider, such as centroxyss, in the Name text box.
How to generate certificate:
- open an editor and copy paste the following :
# This simply generates a self-signed certificate which will import into Secret Server
# Replace the variables below (pass, dnsname, filename)
# Requires .NET 4.5 or above
# Please Run As Administrator
###--Variables to Replace--###
# Certificate Password for PFX
$pass = 'centroxy1234'
# DNS name in certificate
$dnsname = 'secretservercloud.com.sg'
# Filename of PFX
$filename = 'centroxy.PFX'
###--Commands--###
# NOTE: The provider must be set in order to be compatible with .NET 4.5 newer versions of .NET can import certs from more providers
$securepass = ConvertTo-SecureString -String $pass -Force -AsPlainText
$cert = New-SelfSignedCertificate -certstorelocation cert:\localmachine\my -dnsname $dnsname -HashAlgorithm SHA256 -KeyLength 4096 -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider"
$path = 'cert:\localmachine\my\' + $cert.thumbprint
Export-PfxCertificate -cert $path -FilePath $filename -Password $securepass
# remove from cert store
Remove-Item $path
2. Open powershell (Administrator Mode) then enter the commands above and press enter to generate the certificate “centroxy.PFX”.

9. Click the Select Certificate link. The Upload Certificate popup appears:

10. Click the Upload Certificate button to upload the certificate used for SS’s HTTPS configuration.
11. Locate your certificate .pfx file(“C:\Windows\system32\centroxy.PFX”) and select it.
12. Click the Open button. The new certificate appears.
13. Type the access password for the private key of the certificate in the Password (‘centroxy1234’) text box.
14. Click the OK button. The certificate is uploaded and tested, and the popup disappears. The certificate now appears in the SAML Service Provider Settings section.
Note: If you have an outdated version .NET Framework (earlier than 4.6.2), you may see an error recommending you upgrade to fix the error. Reload the certificate after you do so.
15. Click the Save button.
Then upload the “SecretServerSAMLMetadata.xml”


16. Click Save.
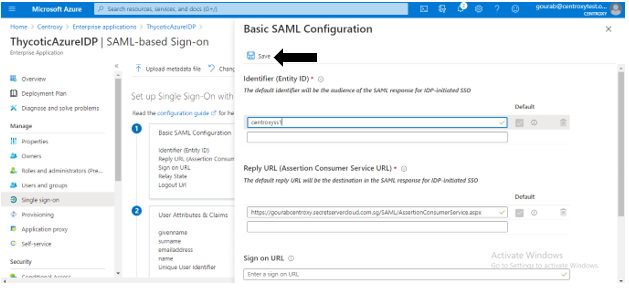
· After saving it Refresh the page and the SAML configuration field and SAML Signing Certificate will auto-populate.


17. Scroll down and click Metadata XML to download the metadata for this application.

18. Go back to Azure Active Directory and click on App registrations

19. Select your Thycotic Azure IdP Application.
. If not immediately visible, you may need to click View all Applications.

20. Click Settings > Properties, then enter the Logout URL field for your instance. The form for this URL will be:
https://yourssname.secretservercloud.com.sg/saml/SLOService.aspx,
21. click Save.

22. Next, navigate to your Secret Server instance and to the Admin > Configuration > SAML page
23. Click Create New Identity Provider

24. Click Import IDP from XML Metadata.

25. Select the Azure AD metadata you saved/downloaded previously.
. If you don’t see it, you might need to change the metadata filetype to .xml

Adding Users to Single Sign-On in Azure AD
Before adding users to your new Single Sign-On system, they need to be synced between Secret Server and Azure AD. You can do this either by adding users directly to Secret Server or Azure and ensuring they match, or by using Secret Server Discovery to sync with existing Azure AD users in bulk. The main point here is that, in order for users to be authenticated by the Single Sign-On workflow you are setting up, usernames must match between an existing user in both Secret Server and Azure AD. Check usernames carefully to ensure they line up between both systems if adding users manually.
1. Log into your portal.azure.com account.
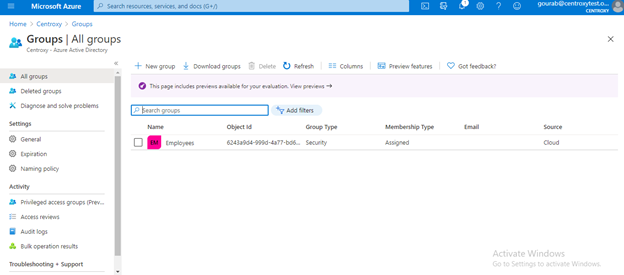
2. Navigate to Azure Active Directory > Enterprise Applications > Select your IDP from the list, then select Groups. Click Add New Group.

Click Create.
3. Click Users and groups/None Selected.
4. Search for the user you want to add to your SAML workflow. (Note that any users added must also exist in your Secret Server instance. Usernames must match between the systems). Click Add members at the bottom, then select.

5. This user should now be able to use the SAML workflow. To test this, login to Azure as the user, then browse to your Secret Server instance. The user should be logged in automatically to Secret Server without prompting for login credentials.
Advanced Settings
The following Secret Server Identity Provider Advanced Settings can be configured in Azure AD
· Click on the app registration and select the application and > Add a Permission.
· Give these following permissions.
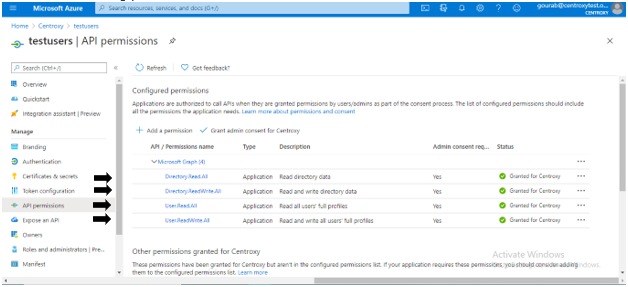
· Then select Grant admin consent .
· Assign “Owner” to the application.

· Then select a user and assign it as an owner .

Final Step is to Integrate the azure AD with secret server AD service
· Go to secret server .
Admin > Directory Services > Add Domain > Azure Active Directory Domain.

· Then go to the Azure portal >Azure AD > App Registration > Overview.

· Then generate a client secret :

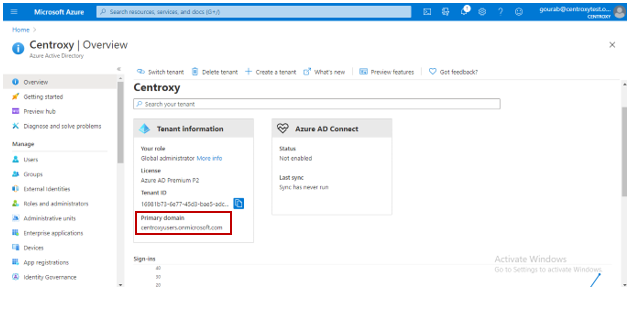
· For the Domain name Go to Azure AD > Overview.
Reference :
https://github.com/thycotic/extrabits/blob/master/Generate-Cert.ps1
https://thycotic.force.com/support/s/article/SS-Setting-up-Azure-AD-for-SAML
https://docs.thycotic.com/ss/10.8.0/authentication/configuring-saml-sso/index.md
